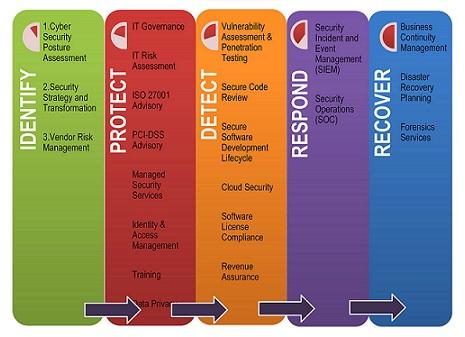
The primary reason for such a disaster recovery document – is to develop a clear bit by bit direction with a timeline for specific roles; its execution supports the following errands:
- Quick recovery of business IT infrastructure after a disaster;
- Guaranteeing the implementation of fundamental IT infrastructure functions during the downtime of the main data center;
- Save organization data.
- External cybersecurity threats;
- Worker errors.
Managing data distribution between two physically separate data centers is necessary to implement a disaster recovery plan. Virtual machine data and formats can be stored or as a disaster recovery system.
DRP plans are anything but static documents; they need to be continually audited and adjusted to the business’s needs. Backup services in the cloud can set up a Disaster Recovery Plan. You can use this format to create a disaster recovery plan all by yourself.
Prepare a cyber-disaster recovery plan
Are you prepared for disaster if things go wrong for your business? For example, what are your procedures for returning to normal employment if malicious perpetrators inject ransomware into your system? The first twenty results from a Google search for “What do I do if I violate cybersecurity” will begin: “See your cybersecurity disaster recovery plan (DRP).” It doesn’t matter how big your business is – just a few simple things can prevent many problems in the event of an accident.
Assign the right people the right responsibilities
It is important to maintain enterprise DRPs, whether they are developed by an internal team or an external contractor.
Whenever a security breach occurs, the first responder should be the person or people who know your company’s DRP inside and out. Your list of the company’s designated respondents should include outside-of-hours contact details (written on Page One of the DRP sent to you). First responders should be provided with assistance in creating and maintaining cybersecurity disaster recovery plans by their departmental heads and critical stakeholders. To ensure cooperation and assistance throughout your organization, first responders will need assistance receiving recognition and attention required by the plan. There is no doubt that cyber security is important, and it should be viewed from top to bottom as a critical business function – not just a source of more employment or inconvenience.
In selecting people who can lead these initiatives, it’s important to find people who are organized, passionate about what they do, and good communicators who can work with people from different departments within your organization with varying levels of technical expertise. In addition, the DRP development, analysis, and maintenance need to be a permanent part of the regular workload of these people.
For an effective cybersecurity DRP, you need input from all areas of your company to identify important departmental needs, critical equipment, and data. A dedicated representative should represent each region, while your DRP cybersecurity leader should coordinate the information and requirements. The representatives of these departments will also be valuable in developing “worst-case scenario” exercises and aiding in establishing friction-free communication lines.
Data and tools that are important to identify
When working in the departments and communicating with team representatives, it is crucial to understand what specific programs, programs, information, and systems are essential to the ongoing performance of each department. Only after gaining this information can operations be effectively restored with minimal downtime.
Also Read:- Write for us Technology
Also Read:- write for us tech
Research the tools and data that are most important to each department to function effectively. Create departments with very different needs. For example, shipping department priorities will differ substantially from the offshore sales team, the finance department, or human resources. Depending on the year, some of these requirements can even change. For instance, some resources are more crucial at the end of the year. In the week before the payment date, payment data may be of even greater importance. For some departments, data usage can even vary from morning to afternoon.
The knowledge of your department is vital to getting the most out of this exercise, and your departmental representatives will provide the necessary information. Be sure to identify the backup location for this important data, how and where key tools and software must be replaced, who needs what levels of access, and their responsibilities.
If the DRP includes a password-encrypted password, it is advisable to print the latest version and store it in a secure location. When your network is compromised, there is no point in having a digital plan.
Being aware of the dangers
Create a list of potential cybersecurity disaster scenarios that may affect your business for your entire organization. By identifying weak points in advance, you can gain insight into your vulnerabilities and mitigate them.
As an example, what would you do if a dissatisfied former employee deleted data before leaving your company? If a virus or malware corrupted important data, how would you react? If you conduct a comprehensive IT audit and investigate backup solutions at that time, you can also account for human error and hardware damage.
By effectively documenting your weaknesses and identifying them, you will solve many problems right now. For example, using runtime protection software, it is possible to stop supply chain attacks, secure managed databases with cloud security solutions, or automate API protection. You should identify your vulnerabilities and document how you would respond. By implementing an advanced DR plan, you can provide a high level of business coherence at a relatively low cost..
Author Bio:
This is Aryan, I am a professional SEO Expert & Write for us technology blog and submit a guest post on different platforms- technootech provides a good opportunity for content writers to submit guest posts on our website. We frequently highlight and tend to showcase guests.